Introduction
The idea of the article arose from the desire to pass certain sites through the VPN tunnel directly through the router, since there are a large number of devices at home, and it is inconvenient to let all traffic through the VPN due to the low bandwidth of the tunnel. The article was written immediately after creating the configuration. The configuration will take place in Winbox MikroTik.
StrongSwan
StrongSwan, .
/etc/ipsec.conf
config setup
charondebug="ike 2, knl 2, cfg 2, net 2, esp 2, dmn 2, mgr 2"
uniqueids=never
conn ikev2-vpn
auto=add
compress=no
type=tunnel
keyexchange=ikev2
fragmentation=yes
forceencaps=yes
dpdaction=clear
dpddelay=300s
rekey=no
left=%any
leftid=
leftcert=server-cert.pem
leftsendcert=always
leftsubnet=0.0.0.0/0
right=%any
rightid=%any
rightauth=eap-mschapv2
rightsourceip=10.10.10.0/24
rightdns=8.8.8.8,8.8.4.4
rightsendcert=never
eap_identity=%identity
/etc/ipsec.secrets
# This file holds shared secrets or RSA private keys for authentication.
# RSA private key for this host, authenticating it to any other host
# which knows the public part.
# this file is managed with debconf and will contain the automatically created $
include /var/lib/strongswan/ipsec.secrets.inc
: RSA "server-key.pem"
user1 : EAP "password1"
user2 : EAP "password2"
iptables VPS
-A FORWARD -s 10.10.10.0/24 -o eth0 -p tcp -m policy --dir in --pol ipsec -m tcp --tcp-flags SYN,RST SYN -m tcpmss --mss 1361:1536 -j TCPMSS --set-mss 1360
-A POSTROUTING -s 10.10.10.0/24 -o eth0 -m policy --dir out --pol ipsec -j ACCEPT
-A POSTROUTING -s 10.10.10.0/24 -o eth0 -j MASQUERADE
-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -p tcp -m tcp --dport 22 -j ACCEPT
-A INPUT -p tcp -m tcp --dport 443 -j ACCEPT
-A INPUT -p tcp -m tcp --dport 80 -j ACCEPT
-A INPUT -i lo -j ACCEPT
-A INPUT -p udp -m udp --dport 500 -j ACCEPT
-A INPUT -p udp -m udp --dport 4500 -j ACCEPT
-A INPUT -j DROP
-A FORWARD -s 10.10.10.0/24 -m policy --dir in --pol ipsec --proto esp -j ACCEPT
-A FORWARD -d 10.10.10.0/24 -m policy --dir out --pol ipsec --proto esp -j ACCEPT
-A FORWARD -j DROP
IPSec MikroTik
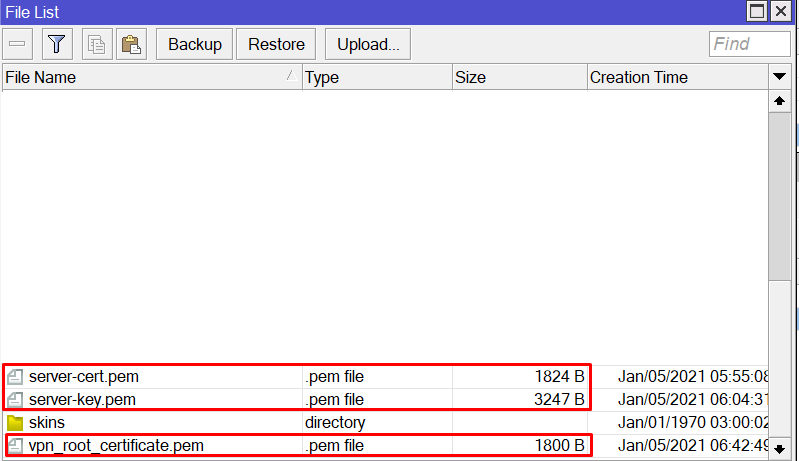
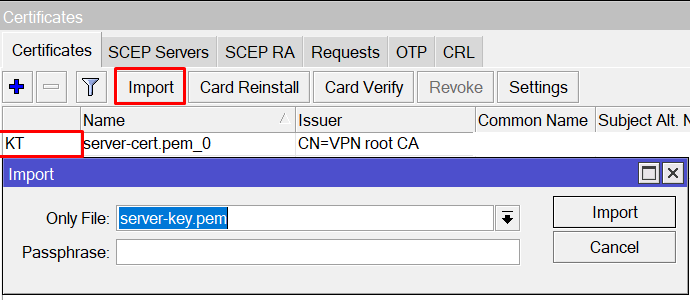
, MikroTik Files.
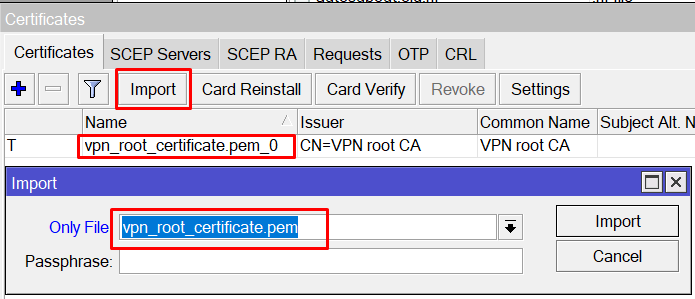
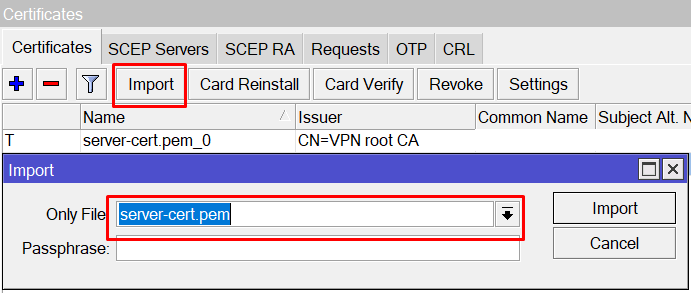
System -> Certificates
VPS StrongSwan.
StrongSwan.
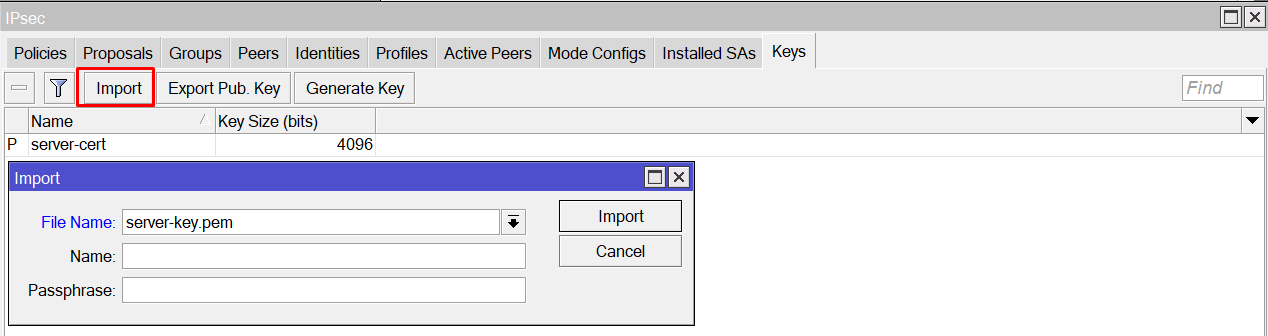
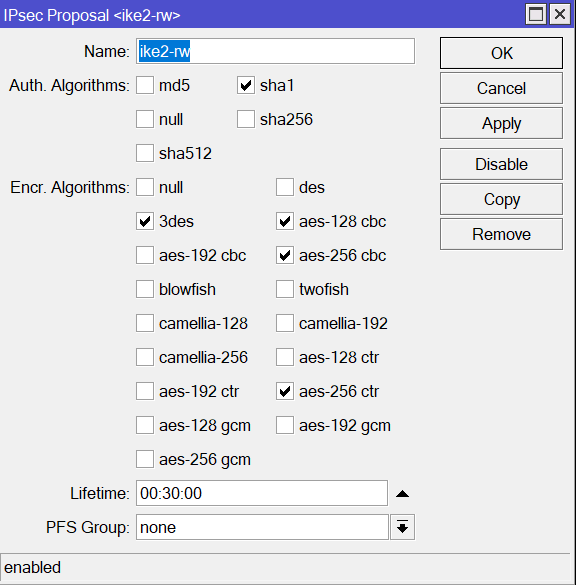
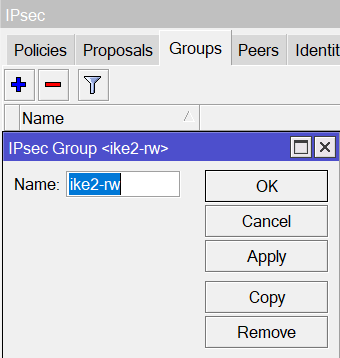
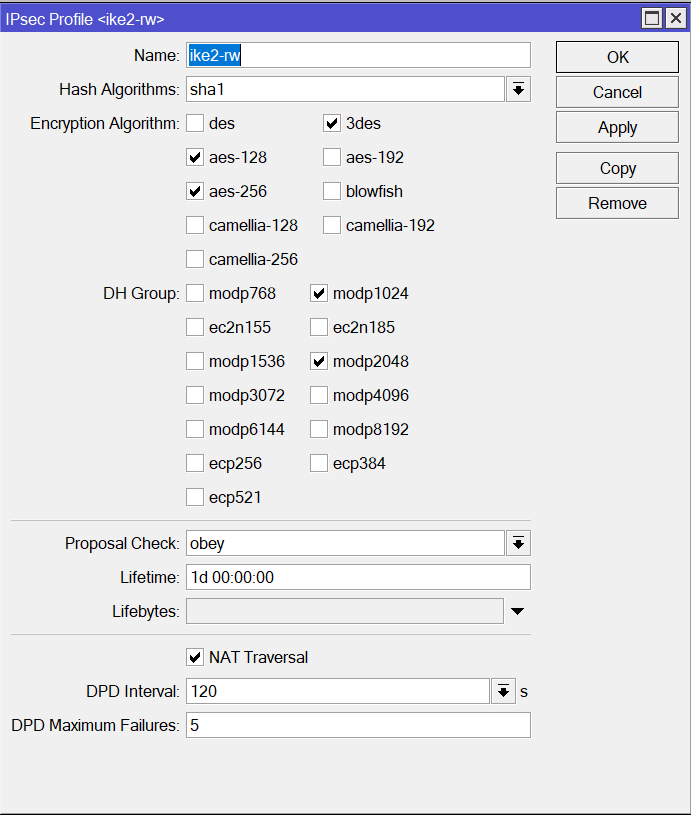
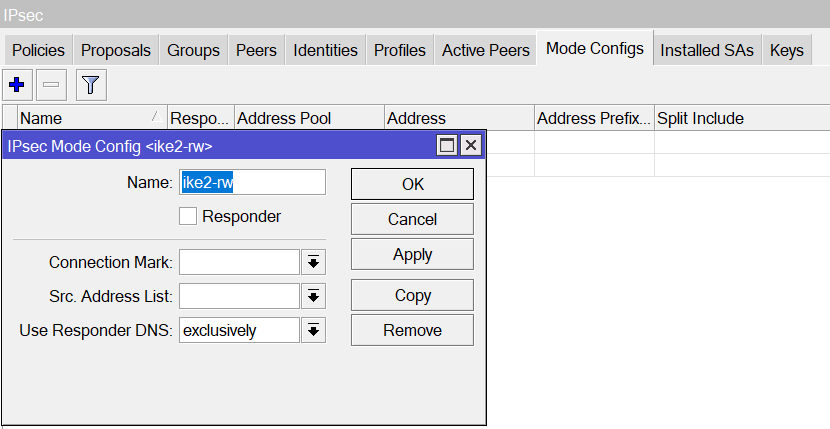
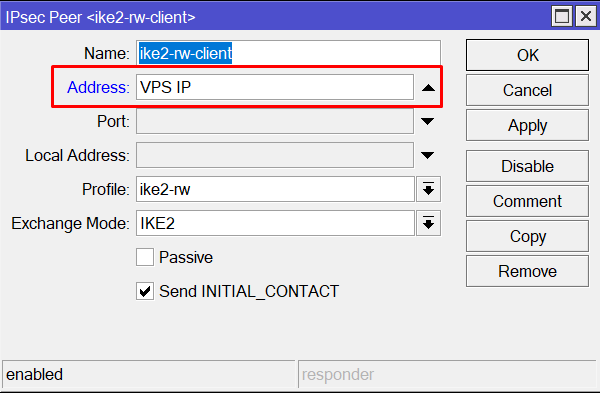
IPsec
IP -> IPsec
StrongSwan, .
, VPN-.
"VPS IP" , StrongSwan.
IPsec Idenity , .
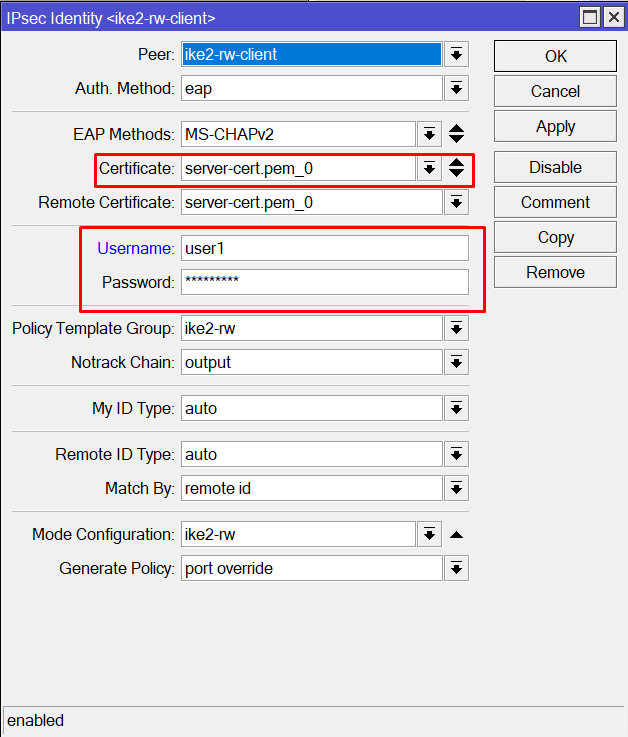
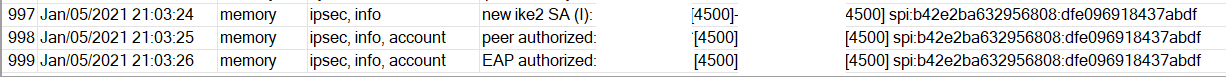
MikroTik StrongSwan .
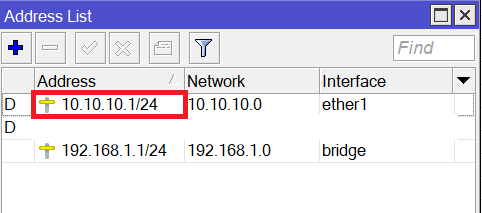
IP -> Addresses , IP StrongSwan.
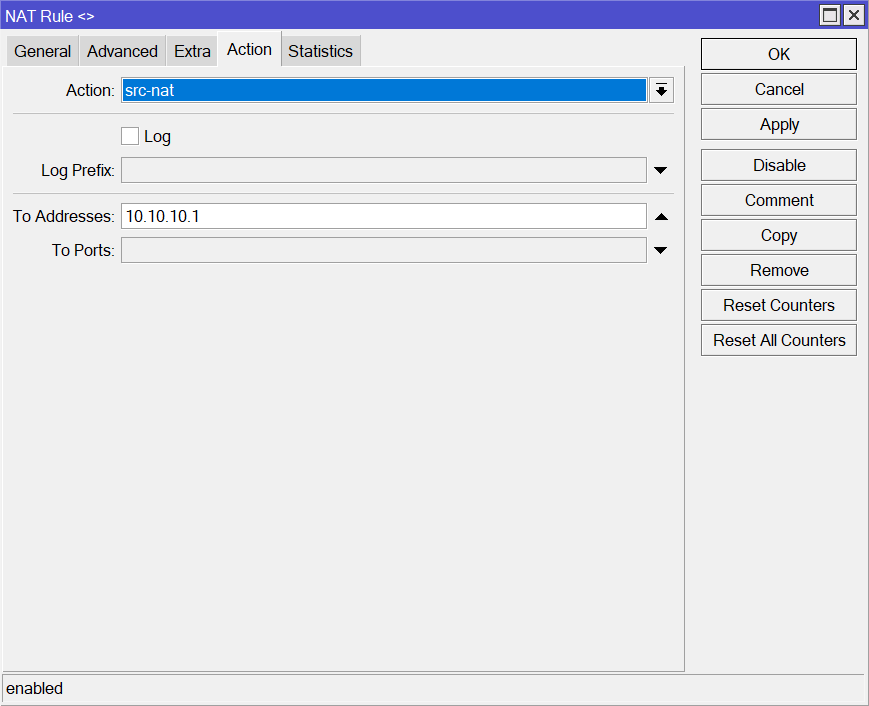
IP -> Firewall
NAT .
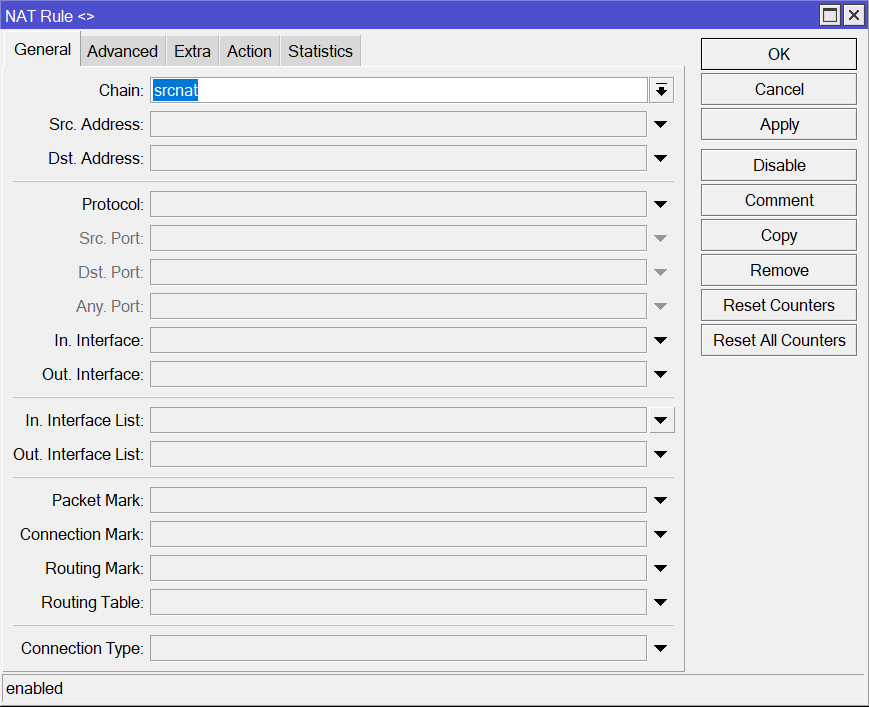
.
local - .
List1 - .
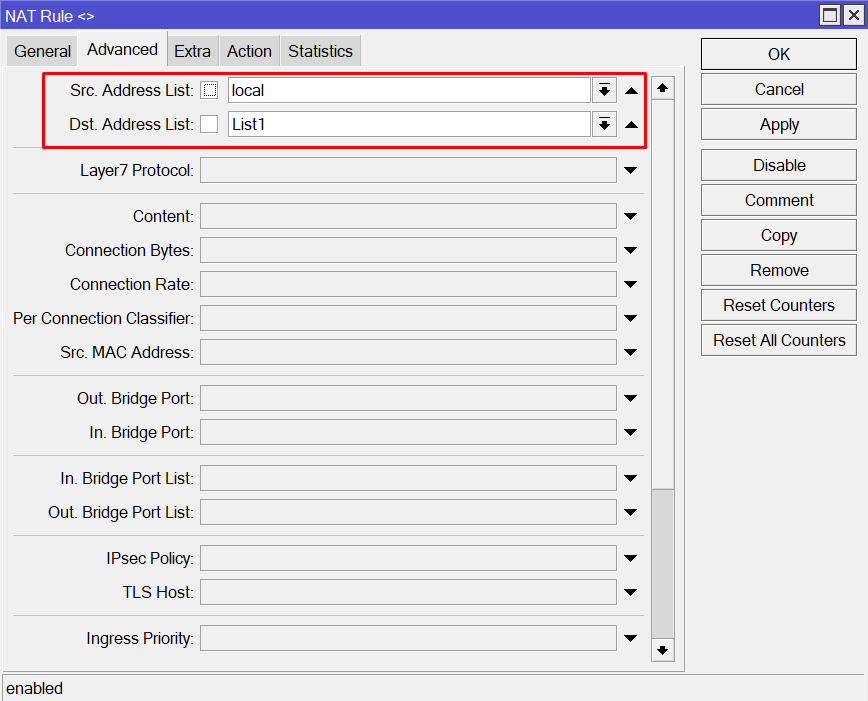
(IP StrongSwan)
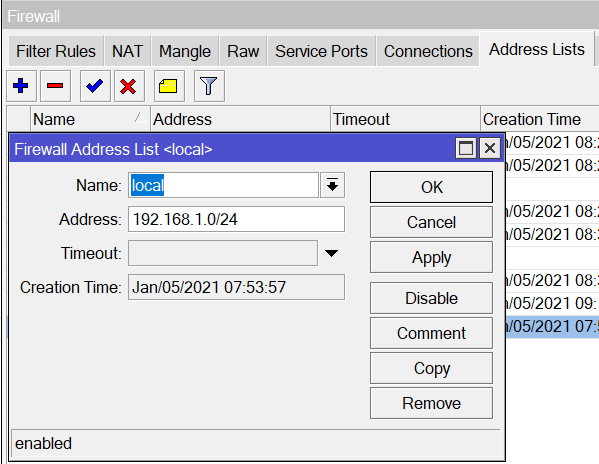
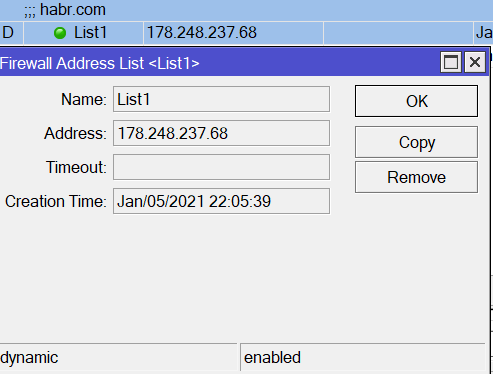
IP -> Firewall
Address Lists :
local - the subnet of the router, in my case 192.168.1.0/24
List1 - list of sites. For example habr.com, you can add a site using fqdn, the ip address will be determined automatically.
List1 - list of sites. For example habr.com, you can add a site using fqdn, the ip address will be determined automatically.
Conclusion
In this article, I tried to describe in detail the configuration of the tunnel between MicroTik and StrongSwan. I really look forward to your feedback and your constructive criticism.