
In this article, you will learn:
What are secret sharing schemes and what they are eaten with
Why threshold schemes are good
The idea of the Mignott scheme
Carnin-Green-Hellman scheme idea
Where such schemes are applied
What are secret sharing schemes and why are they needed?
, "Gent und seine Schönheiten". , . , , - , - , - ... , – . , . . , , .
. , , . , .
. " ", , .
:
- ,
- ,
-
- ́
. , ? ?
, , (t, n) . n , , t . t-1 , . , , , .
, n , , t n . , , , t, .
. :
,
,





. ,

,
.
, :
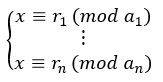
–
,
, n – ,
.
, . , S.
.
.
t . :
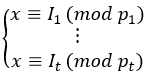
,
. t-1 , ,
– t-1 . , , ,
.
, , , . , , . , – .
--
, c t , , t . . n+2 t , t x t, , t ( ).
. S
–
.
t t U:
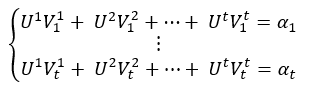
, , . U, .
, t , . , -- . , t , .
(t, n) . , t , . , , .
To create threshold cryptosystems, such open encryption systems can be used, such as:
Cryptosystem RSA
El Gamal Cryptosystem
Threshold cryptosystems are used in many areas, for example, for storing the secret key of a certification authority, in government and military areas, cloud environments and electronic voting schemes.
Sources
Karnin E. D., Greene J. W., Hellman M. E. “On Secret Sharing Systems” // IEEE, 1983.
Schneier B. “Applied Cryptography. Protocols, algorithms, source texts in the C language ”- Triumph, 2002
https://ru.wikipedia.org/wiki/Sharing_Secret
http://cryptowiki.net/index.php?title=Secret_Sharing Schemes._Threshold_Cryptography