TL; DR:
VoLTE seems to be even less secure than the first Wi-Fi clients with WEP. Exceptionally architectural miscalculation that allows you to XOR a little traffic and recover the key. The attack is possible if you are near the caller and he often makes calls.
Thanks for the tip and TL; DR Klukonin
, , . , VoLTE .
(Matthew Green).
. , , . .
It has been a long time since I wrote an attack of the week post , and it upset me. Not because there were no attacks, but mainly because there was no attack on something widely used enough to get me out of my creative crisis.
But today I stumbled upon an interesting attack called ReVoLTE on the protocols, the hacking of which especially pleases me, namely, the protocols of cellular networks (voice over) LTE. I am delighted with these particular protocols - and this new attack - because it is very rare to see real protocols and cellular network implementations hacked. Mainly because these standards were developed in smoky rooms and documented in 12,000-page documents that not every researcher can master. Moreover, the implementation of these attacks forces researchers to use sophisticated radio protocols.
Thus, serious cryptographic vulnerabilities could spread all over the world, and possibly only be exploited by governments before any researcher pays attention to them. But there are exceptions from time to time, and today's attack is one of them.
The attackers are David Rupprecht, Katharina Kohls, Thorsten Holz and Christina Pöpper of the Ruhr University in Bochum and New York University Abu Dhabi. This is a great attack on re-installing a key in a voice protocol that you are probably already using (assuming you are from the older generation who still make phone calls with a mobile phone).
To begin with, a brief historical excursion.
What is LTE and VoLTE?
80- Global System for Mobile ( ). GSM , , , . GSM , .
, , Long Term Evolution (LTE) . LTE , GSM, EDGE HSPA . , TL;DR , LTE – , 5G.
, , (IP) , , «» «» . . , LTE Voice-over-LTE (VoLTE), IP- LTE, . VoIP-, VoLTE- . ( ) , .
VoIP, VoLTE IP: (Session Initiation Protocol – SIP) , (Real Time Transport Protocol, RTTP, RTP) . VoLTE , .
, ?
LTE, GSM, . ( « », UE) ( , ). , . .
( , VoLTE , , VoLTE , . , , . ).
GSM : , , ( , , «Stingray») . LTE , .
. , — — «EEA» ( , AES). , CTR, :
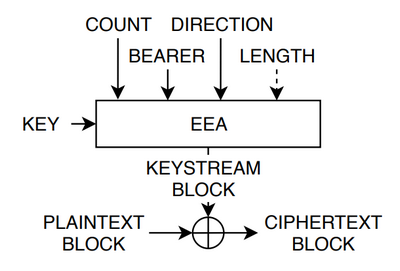
VoLTE (: ReVoLTE). EEA – , «COUNT» – 32- , «BEARER» — , VoLTE -. «DIRECTION» , – UE .
(EEA) AES, , - , GSM. , , .
: LTE () , , — , «bearer» «direction» — - . – « nonce», - . , - .
nonce CTR- , Poison
, LTE : « , ». LTE 7000 , , , . , . , XOR- . , .
ReVoLTE?
ReVoLTE , . , VoLTE, , , , « ». ( (Raza & Lu), . ReVoLTE ).
, .
, LTE , LTE . , VoLTE , 2 [ OSI – .]. .
, LTE «bearer». Bearer – , . - ( Twitter Snapchat) bearer. SIP VoIP , . LTE, , , LTE QoS ( ), : .. TCP Facebook , .
- , . LTE «bearer». , , . , , . , LTE - « , bearer ». , .
, , , — , () bearer. , , , . . , , , , , , .
, , . , , . .
. , , - «» , . , - . , XOR .
, . , , , , . , , , . , , – , .
, :
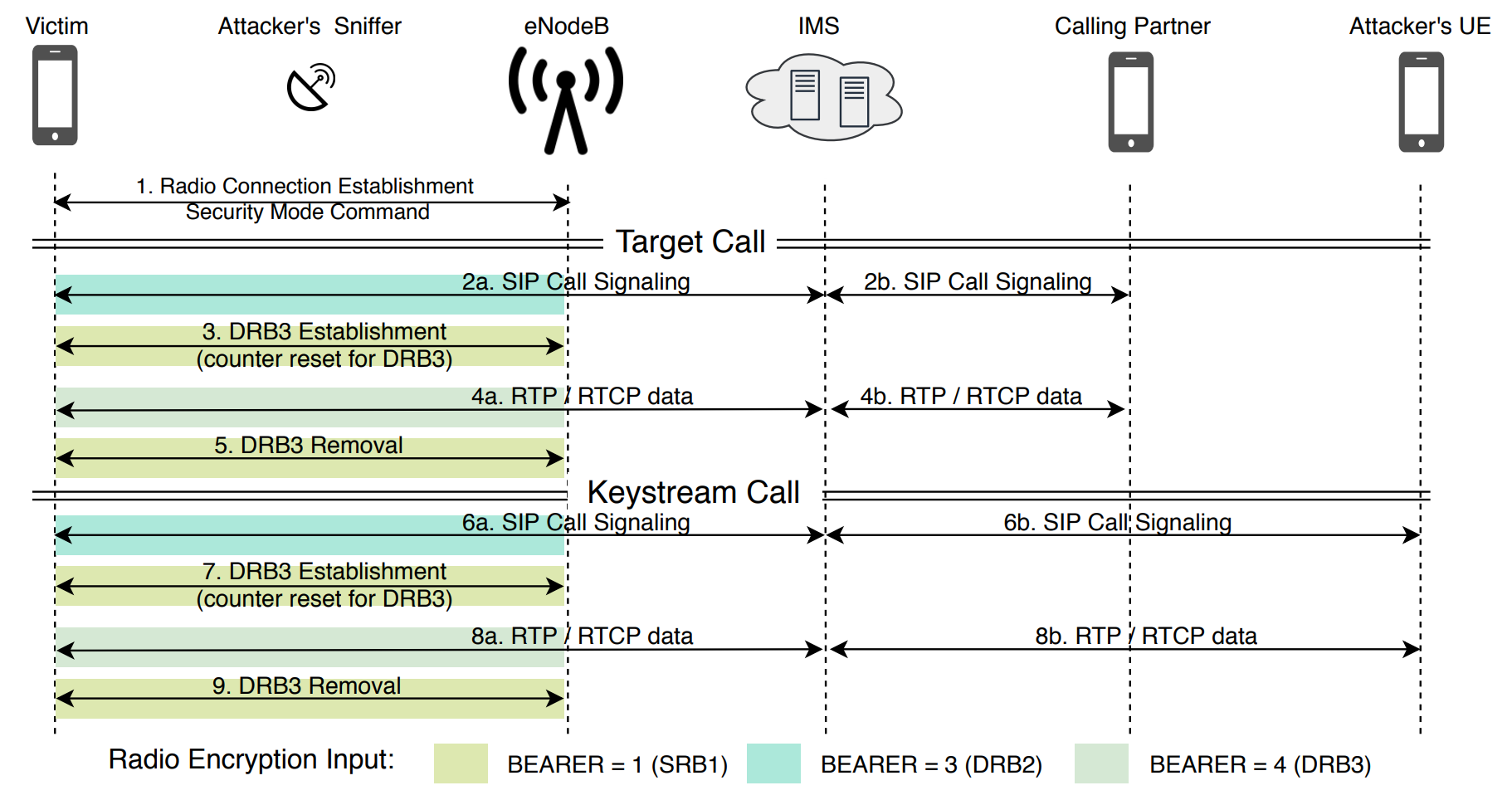
ReVoLTE. , . ( ), , .
?
, ReVoLTE. , . :
- ( ) VoLTE-?
- LTE- ?
- , ?
- , – , , () , «», ?
ReVoLTE . - Airscope VoLTE . ( , , , - – ).
, , – , . , , – «», .. SIP- .
, (4) – , . , , . , , , , . LTE RTP, RTP-.
, , , , . , (.. ), .
«real world attack» . – , , , 89% . , .
, , , , , .
?
: () , . , , . !
, . , , , . , , .
, nonce . , , , , , , 5G - .
, , . , WPA2, , , , ? , . () , .
, , Facebook Apple: , OSI, . , WhatsApp Signal FaceTime, , . ( ) . , , .
, : .